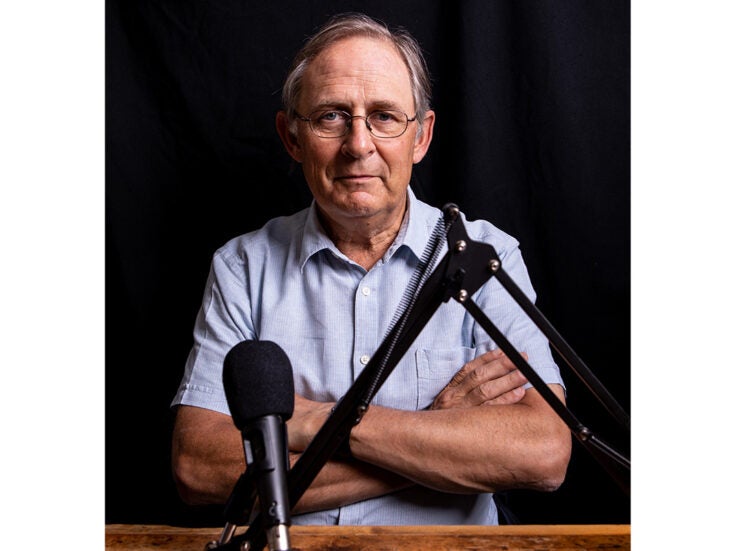
Nigel West shows us how the proliferation of everyday electronic gadgets in our lives has left us scarily vulnerable to surveillance.
Much of the technology that is now taken for granted has its origins in developments introduced in Northern Ireland three decades ago to monitor the activities of suspected terrorists. The remote number-plate recognition system, now a daily feature of life in the Congestion Charge Zone in London, has its origins in a classified project bench-tested in Ulster, wherein the requirement was to identify a car moving at 80 miles an hour at night in the rain, south of Belfast.
The result was a database, accessible by security personnel down to soldiers manning vehicle checkpoints, which provided an instant computer-generated trace of sightings over the past six months. As the collective effort was clandestine, with the sensors often disguised as motorway gantries, road signs and Gatso traffic cameras, few realised the scale of the monitoring operation which was later extended to airport approach roads, and is now widely available for revenue generation.
Text messaging, now an essential part of modern life, has its origins in DISCUS, a super-secret CIA gadget created to enable spies to communicate with their case officers in what was termed in the Cold War ‘denied territory’, where a rendezvous was too risky. DISCUS enabled an agent to transmit a low-powered enciphered message from a car or bus passing close to the diplomatic premises accommodating the CIA station, and was used to great effect by Colonel Ryszard Kuklinski, the Polish mole who betrayed Soviet plans for the imposition of martial law in Warsaw in 1979.
The DISCUS derivative is today’s mobile phone, an instrument which can provide a cornucopia of intelligence to anyone with the right analytical equipment. The SIM card contains details of past calls and SMS texting, even those that supposedly have been deleted, and plenty more besides.
Many countries now require service providers to retain records for several years and, unless the battery is removed, a mobile phone provides an accurate forensic record of the owner’s whereabouts at any time on any date. Access to the handset itself can also reveal, through microscopic DNA samples recovered from the microphone, the true identity of all those who have ever used it.
Thus all mobile phones have their own individual characteristics, and their serial numbers can be retrieved simply by dialling *#06#, which reveals a vital seventeen digit figure that, when reported in the event of its loss, will prevent it from being used by a thief.
The intelligence value of mobile phones was proved when one of the July 2005 bombers in London fled to Rome by train, and his journey was monitored continuously, in real time. In August 2007, the retrieval of two handsets, switched to vibrate and intended to be used as detonators, from two car bombs in central London, provided crucial clues to a terrorist ring and led detectives to other suspects in Glasgow.
Clearly Al-Qaeda hadn’t learned the lesson of the Madrid train bombs of March 2004, when the culprits were identified from a single mobile phone switched to alarm clock mode, but set to vibrate at the wrong time. The others went off simultaneously, completing electric circuits that detonated explosives, killing 191 passengers.
Italian police relied on less sophisticated mobile phone analysis when they investigated the abduction of a terrorist suspect in a Milan street in February 2003. One computer programme sorted through 10,718 calls made in the vicinity of the local mobile base station on the day Abu Omar was lifted by the CIA, and linked eleven separate accounts.
Tracing their calls compromised almost all the members of a covert CIA team sent to Italy under alias to supervise the ‘special rendition’, and even revealed their true names because they had claimed their frequent flyer mileage, used credit cards with sequential numbers and stayed in the same hotels. Worse, their call traffic had contaminated the local CIA station housed in the consulate, and its staff who had been working under diplomatic cover.
GPS equipment also retains data on the owner’s movements, and contains a chip that provides an even more accurate record than a mobile phone of where it has been. When installed in vehicles, the equipment amounts to a totally reliable source of potentially vital information. The technology’s potential as a surveillance aid was first disclosed in the movie Goldfinger, when James Bond tracked his quarry across Europe using a rolling map installed in 007’s famous silver Aston Martin DB5, having installed a miniaturised electronic beacon in Auric Goldfinger’s vintage Rolls-Royce.
Celebrities, of course, are familiar with the hazards of disposing of their household waste in outside bins, and the CIA learned during the 1979 Tehran hostage crisis that mere shredding is not a guarantee of destruction, especially if there are Islamic students willing to devote hours reconstructing the strips of paper into readable documents. Anyone conscious of their own security will burn their bank and credit card statements, and any other sensitive correspondence they would rather not have read by others.
For the security authorities, developing a profile of a potential target is simply a matter of joining the dots, of which there are plenty. How is it possible to remain invisible from tax, social security, driver’s license, electoral roll, Land Registry, Companies House, vehicle taxation, motor insurance, television licensing, utilities, rates, email, machine-readable passports, frequent flyer accounts, medical records, congestion charging, credit ratings, ATM withdrawals, travel cards and all the other essential paraphernalia of modern life? Much of this information is freely available and unprotected by legislation intended to limit unauthorised intrusion, but often serves to facilitate access for professional snoops.
During the Cold War, counter-intelligence experts dreamed up a variety of ingenious devices to eavesdrop without the need to install bugs, to track cars from overhead aircraft using invisible ultra-violet paint sprayed on vehicle roofs, and to remotely transform limousines into satellite-connected recording studios as they passed through specially constructed choke-points. Some of the equipment, powered from independent supplies, can take experts many hours to detect. Indeed, when Gerry Adams commanded the Provisional IRA in Belfast he did not find the hardware that had been concealed in his car for months.
The West hasn’t exercised any monopoly over advanced listening equipment. The Russian inventor of the Moog Synthesiser also created for the KGB a modulating diaphragm, hidden inside a wooden carving that, when bombarded with radio waves at a particular frequency, transmitted voices over a few hundred yards, without any external power source. Known as the cavity resonance microphone, one operated in the US ambassador’s study in Moscow for five years before it was discovered, leaving technicians awed by its advanced construction.
Proof of the debt owed to the spooks for modern technology may be found in the Apple computer logo, a homage to the death of Alan Turing, the designer of the COLOSSUS, the first programmable analogue computer. Turing committed suicide in 1954, aged 42, by biting into an apple laced with cyanide. His invention, a ‘thinking machine’, was deployed in 1944 to solve supposedly unbreakable Nazi ciphers, and much of his work remained classified until 1977.
His legacy is a world of laptops, internet cafés, GPS and text, not to mention ECHELON discrimination, which allows calls made to and from suspect phone numbers to be intercepted irrespective of location or legal jurisdiction. This allows the US National Security Agency and its British equivalent, GCHQ, to tap into any microwave or satellite communications carrier, almost anywhere on earth.
Awareness of a potential adversary’s capabilities is the first step in taking personal security precautions, the counter-measures. This tradecraft was known in the KGB as konspiratsia, but in a competitive modern environment it is simply common sense.